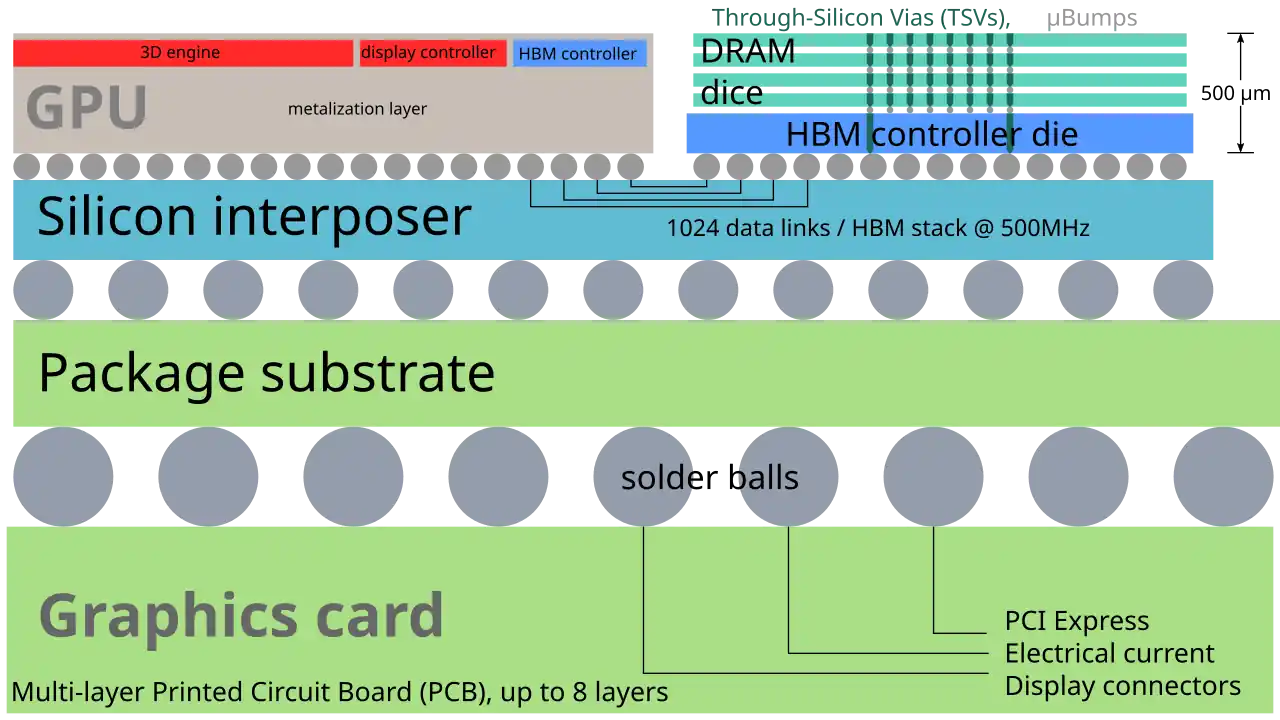
Beyond Binary: The Mathematical Efficiency of Ternary Computing
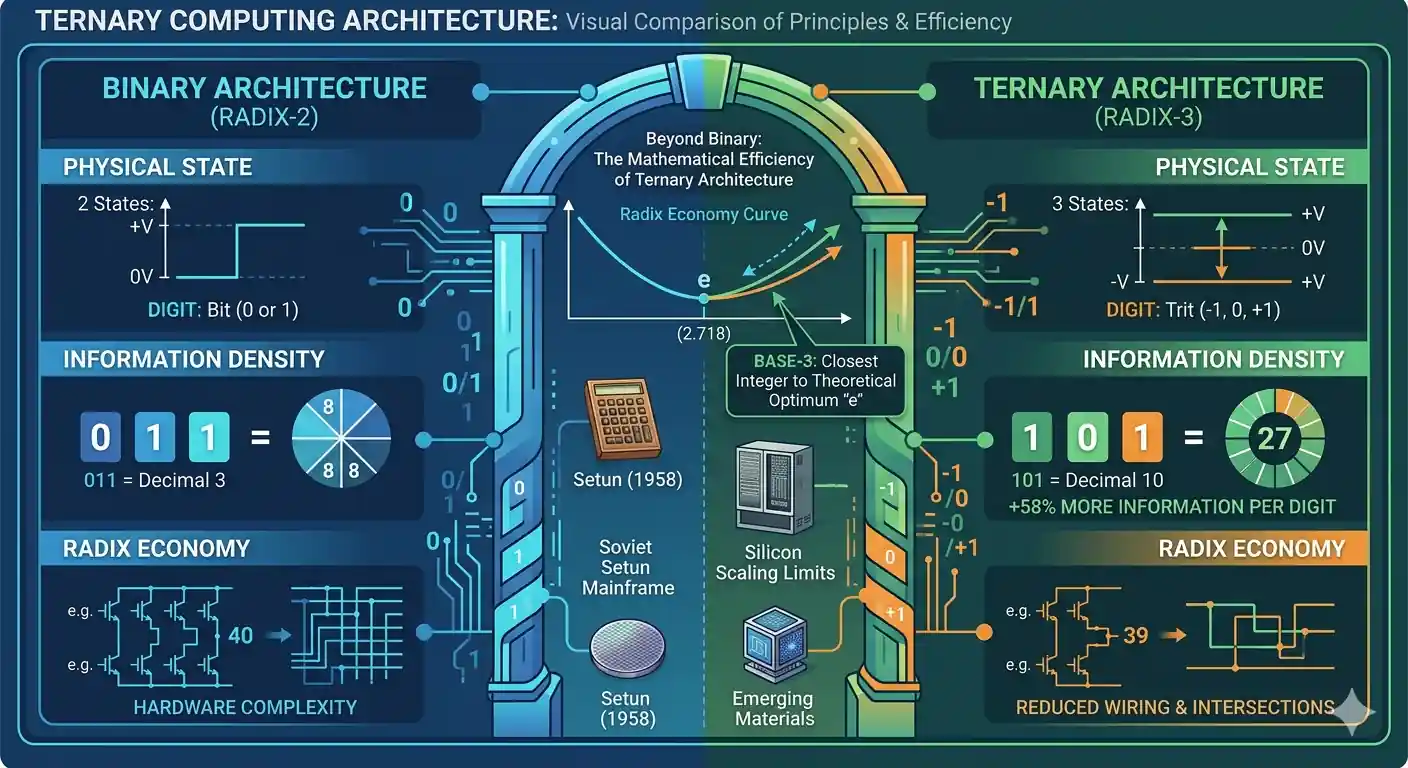
As silicon chips hit physical limits, ternary computing architecture offers a highly efficient alternative to binary. By replacing bits with three-state “trits,” it aligns with the mathematical ideal for processing efficiency. This structural shift yields a 58% leap in information density, simplifies internal wiring, and promises massive energy savings for data-heavy workloads.